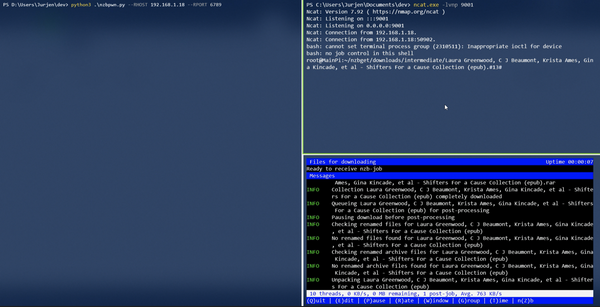
mitmproxy + wireguard + iPhone = quickly discovered insecure endpoints
Recently I stumbled upon mitmproxy and read about their new WireGuard mode. This new mode promises to be an easy way to create a transparent network proxy. During my lunch break, I figured out how easy it is to set up, found an insecure S3 bucket, and still had time to eat lunch and have a coffee.
The setup
For testing, I used my trusted Ubuntu machine and an iPhone 12 running the latest iOS version. These devices were all on the same LAN. mitmproxy was installed with apt install mitmproxy and worked everything out of the box.
A 17-second video in the blog post about the new mode shows how to configure an Android phone to use the WireGuard VPN server. This aligned with my experience setting up the iPhone.
- Run mitmproxy
mitmweb --mode wireguard - Use the WireGuard app to scan the QR code and configure the connection
- Browse to http://mitm.it and follow the instructions.
Finding the insecure endpoint
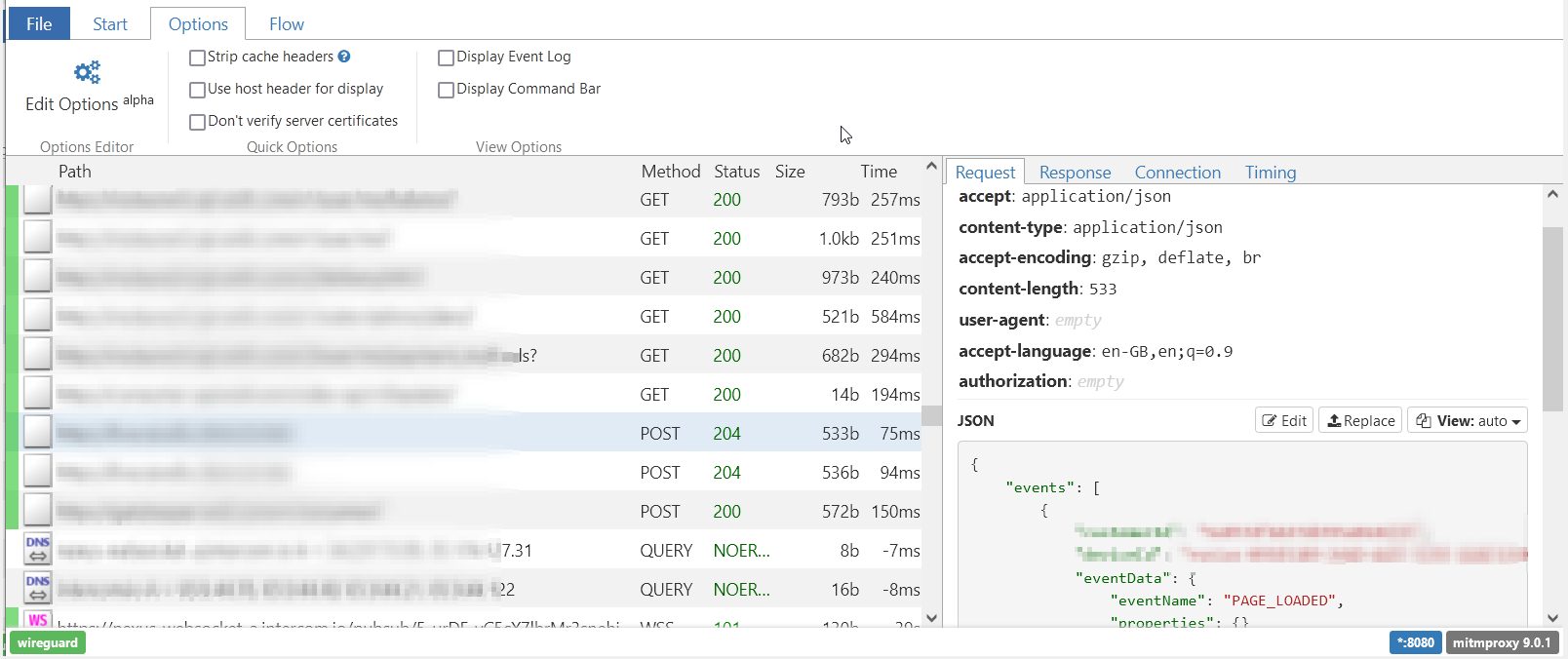
After setting up everything, I started opening a few apps and saw the traffic flow in mitmproxy. It was able to display HTTP, DNS, TCP, and UDP traffic generated by these apps. I was surprised to see that only a few applications implemented certificate pinning, and most of these were finance-related.
While opening several apps, I noticed a classic mistake: a file being requested from an S3 bucket. On further inspection found out that the S3 bucket was left open and hosting PII.
From reading the blog to finding the endpoint in just a couple of minutes, leaving me with plenty of time left to eat and relax. ;)
Afterthoughts
mitmproxy looks like a powerful tool to keep in my arsenal, the ease of use of the Wireguard mode is a huge benefit. So thank you, Fabio Valentini, for your work! I will definitely spend more time looking at the possibilities in more depth.
Several interesting add-ons have been created showcasing the potential power of the tool. There is even a tool called mitmproxy2swagger, that uses mitmproxy captures to create openAPI 3 specs. I can think of several interesting projects that could make use of mitmproxy. Let's see what it will be used for in the future.